4 More Takeaways From Planet Cybersec 2025, Part 2
Bryan Becker, Fractional Chief Information Security Officer, CEO of Class IV
One of the first questions Bryan asked the audience was: Do you know an information security leader who left because they had no support, in budget or personnel?
Did they develop a drinking problem? Did they start seeing a therapist…?
Maybe they had a deal in place, but then a non-security executive, or the Chief Information Officer, shut it down.
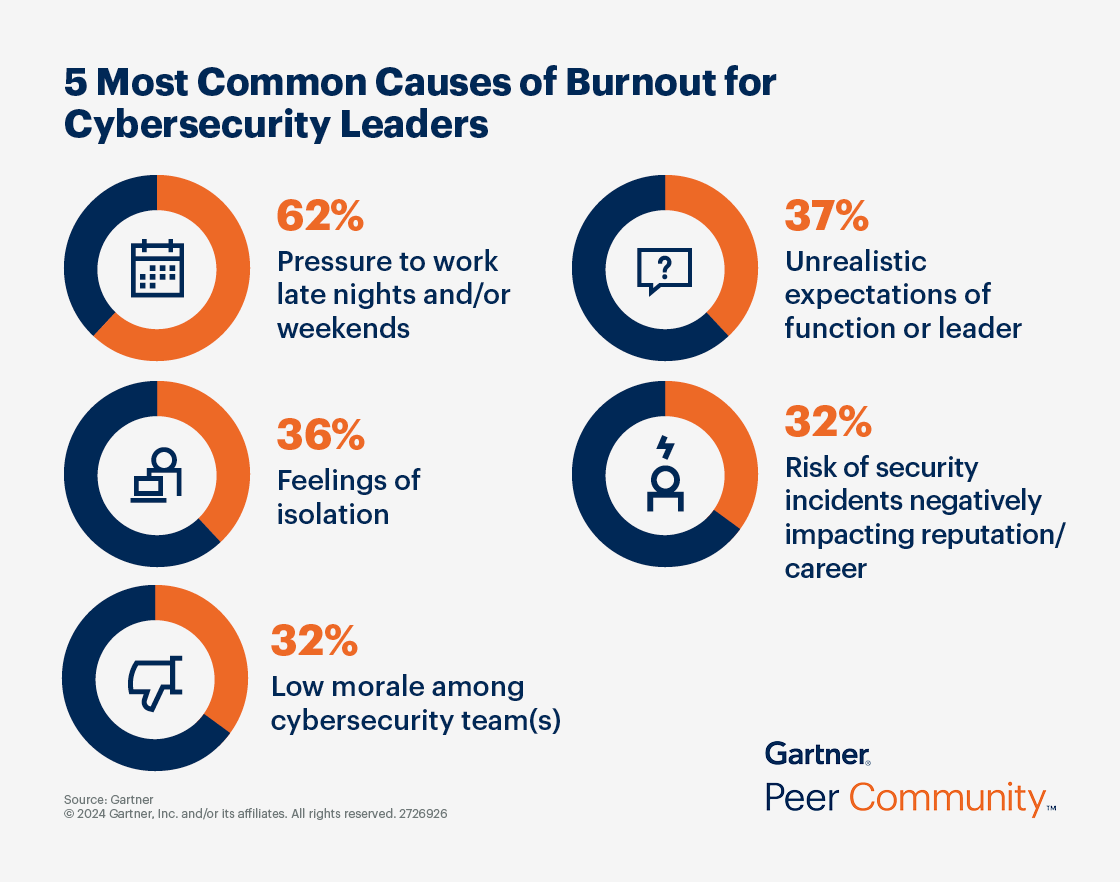
Gartner Peer Community, “5 Most Common Causes Of Burnout For Cybersecurity Leaders”
I like how prepared Bryan was with his slides, citing sources like Gartner, because I was ready to take notes. I never worked in information security, but I have multiple IT certifications and have taught cybersecurity at Per Scholas, so I was able to follow along.
I found this quote he said to be funny:
“If pressure made diamonds, we’d all be rich”
One of my favorite statistics that he shared was 77% of Chief Information Security Officers are terrified of a breach, because then they would be fired. How is it the CISO’s fault that Sally in HR clicked a link and did not follow directions about avoiding phishing like the security training said? I later found the statistic on CSO Online, article titled “77% of CISOs fear next big breach will get them fired.”
CISOs are seen as a “cost center” or a “fall guy,” and the SEC is now getting involved with information security to protect shareholders.
So why would anyone want this job of CISO?
Bryan quoted Alice in Wonderland, a book I really should read one day. "It takes all the running you can do, to keep in the same place."
You need constant effort just to maintain your current position—if you stop moving, you fall behind. And 2025 is no different.
Weighing on the CIO’s mind in March 2025 is new tech Artificial Intelligence, Low-Code/No-Code, Generative AI. There are new laws from a lot of states, on top of federal laws and executive orders.
The CISO role is broken. A “widow-maker” job.
So how can we make this career doable and not destroy you?
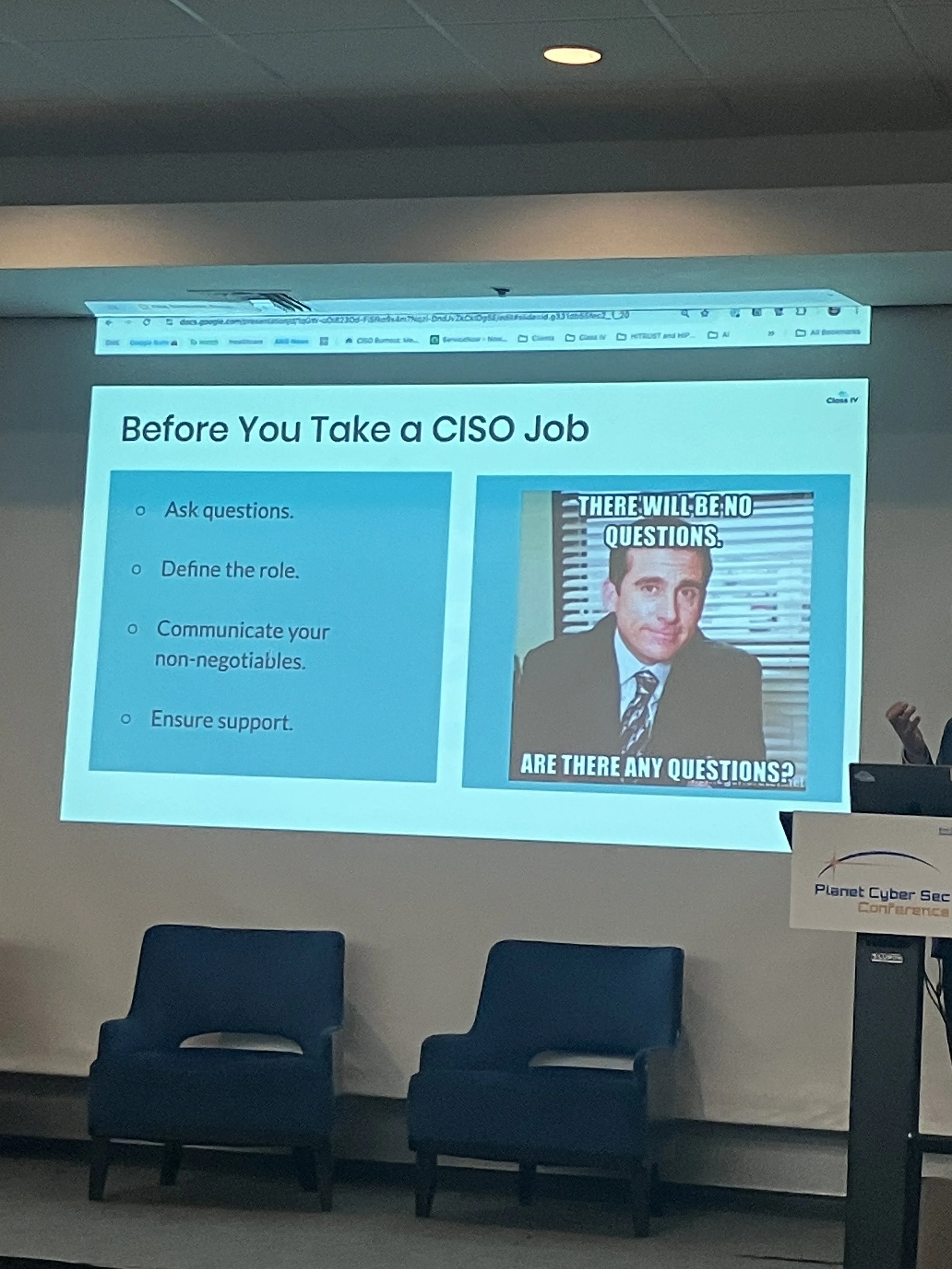
From the Class IV presentation that Bryan did at Planet Cyber Sec 2025
Bryan presented us with some questions that we can ask before pursuing a career in information security.
Takeaway 1: For all situations, know thyself
Some people want 14 hour workdays. That’s cool.
Other people want to work 8 hours, then go home to family.
Bryan says to Set your non negotiables, and work from there.
I honestly find this to be great advice and it was great to hear it. I like to work myself, but I also like my time to relax. I know I would be highly motivated to work towards something I build with my own hands. But to each their own.
Takeaway 2: Get Support Enforcing Security Policy
Can I set policies that must be enforced? Who reports to me as the CISO? Who does the CISO report to?
Will I be on the company director and officer insurance, so the company will protect me if I am sued? Do I have a separate information security budget known to the board that I control?
Bryan suggests to get this in writing and go from there. The paycheck and fancy title may be worth it if you can get these things you need.
Takeaway 3: The best way to get cybersecurity funding is to have a breach.
I thought about this on a personal level, and if I ever got hacked and it caused me to end up embarrassed, or lose a lot of money, I would look at everything “left of boom” to prevent that from ever happening again.
The same goes for an organization: if there is a breach because of phishing, you better believe the CISO is getting funding for cybersecurity, more staff security training, new security policies and so on.
Bryan ends with a question that the CISO will have to answer in a new role:
Takeaway 4: Do you want to be right, or do you want to be paid?
It was a thought-provoking statement. There is definitely a tension between security best practices and business priorities. A CISO might know the absolute right way to secure an organization, but if their approach is too rigid or costly, leadership might not buy in, or even see it as a “cost center” like he talked about before.